297 reads
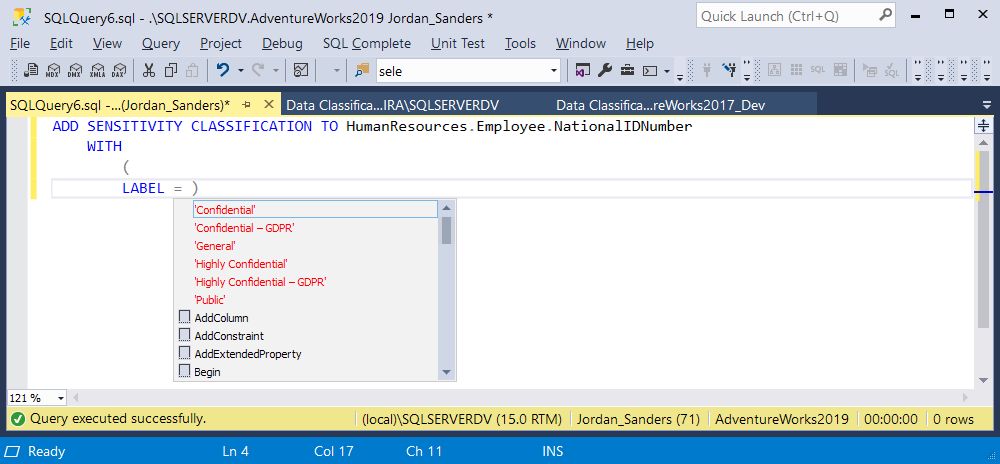
How To Add Data Sensitivity Classification Command in SQL Server 2019
by
October 18th, 2020
PR Manager at Devart since 2010 | Obsessed with the promotion of database development optimization
About Author
PR Manager at Devart since 2010 | Obsessed with the promotion of database development optimization